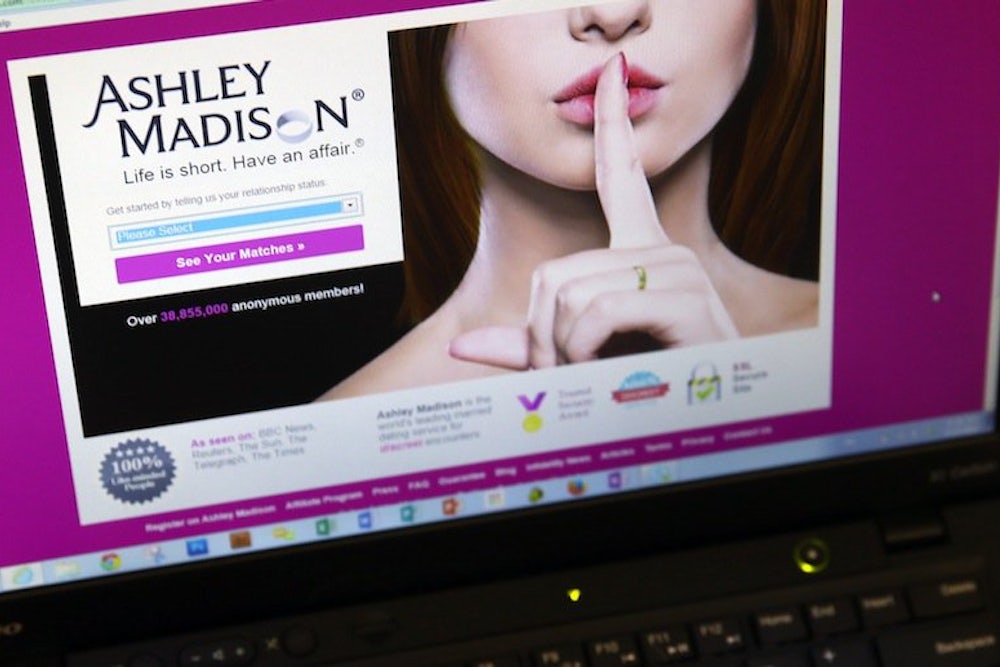
A few days ago I received an email with the subject line “Urgent Lonely Blonde Request.” Urgent lonely blondes do not usually make requests of me, and they don’t usually make it through my spam filter. The blonde in question was a putative Vickie Greer, who explained in a couple of admirably concise sentences that she was young, erotically aroused, and would like to come over right now. She did not explain what a lass with a German email address was doing in Boulder, Colorado. I didn’t click on the link. Instead I forwarded the email to my wife, a professor of family law, with a note that read, “Am I receiving this because of the ‘research’ you’ve been doing on Ashley Madison from our home IP address?”
“Hmmm,” my wife wrote back. “Maybe I should check whether you’re in the database.” Not long afterward, I came across a story about the blackmail emails that some Ashley Madison members were getting—“sextortion” is the clever neologism. Buried deep in the article, a cyber-security expert said members could also expect to be bombarded with email solicitations for sexual services.
It seemed an unlikely coincidence to be getting these missives, just after the Ashley Madison data were leaked. And yet I was emphatically not an Ashley Madison member and couldn’t be on the cheat sheet. Or could I? I dismissed the thought, but it recurred. I soon found myself at one of the newly arisen websites that let people check whether an email address is in the Madisonian data dump. I typed in my address but hesitated before clicking Enter. It felt in some way dirtying, like going to a pawn shop in a bad part of town to retrieve a stolen watch. Even worse was the result: my email was there.
The chief question my wife and I have is: How did I end up in Ashley Madison’s dump pile at all? We have yet to find out, but we have several theories. (Happily, my wife did not for a minute think me unfaithful, just as I would not have doubted her; it’s that kind of marriage.) One possibility is that identity thieves put me in the database. It’s well known, of course, that many of the female members’ profiles on Ashley Madison were fabricated, because the site’s users were disproportionately male. But it is less widely reported that some of the email addresses attached to those accounts may well be the email addresses of real people; addresses can be bought in bulk for around 20 cents each from marketing companies. It is not even necessary for the appropriated addresses to have a woman’s name in them—a man’s name will do just as well—because the addresses attached to the fake profile can’t be seen by anyone but the account holder. Some men (and their spouses) have reported their emails were used in just this way.
Another possibility is that someone who doesn’t much care for me used my email address out of spite when setting up his own account. I have, in fact, encountered this form of identity theft before. Last year pirates posted free, downloadable copies of one of my books on several torrents around the web. I emailed the hosts of those torrents with demands they take the book down, demands which I thought had been ignored. But a few days later my inbox began to overflow with all manner of spam from mostly European domains, a flow that continues, in somewhat diminished form, to this day. Clearly a retaliatory pirate had sent my email to some sort of spam central. I have also written many articles about politics that have drawn impressively enraged replies, occasionally accompanied with threats of bodily harm. In short, I have enemies.
On the other hand, there must be very few people who would be so outraged by a writer of slender renown who, when wracking their brains for a fake email to put on their dirty-weekend accounts, would choose my address instead of that of a more famous target. And of course there other, more immediately gratifying targets to choose from: bosses or teachers, employees or ex-lovers, the uncle with repulsive politics, the neighbor who runs his lawnmower every Saturday at dawn. The media haven’t said much about such innocents, but surely they populate the cheat sheet in numbers that are not trivial.
A third possible explanation of how I landed on the sheet is that, just perhaps, I did sign up for Ashley Madison. Some years ago, I wrote a book about the CIA’s illegal kidnapping and torture of an alleged terrorist in Italy. Over several years, I tracked down ten or so undercover operatives behind the crime, largely by comparing scraps of data they scattered about Italy with similar data on the web. If a spy used a pseudonym to check into a hotel in Milan, and the pseudonym matched a username on a chat board for Corvette lovers, I went to the site and paged through the relevant posts, then went to similar sites and did the same. A lot of those sites required users to set up accounts before viewing their pages, and many were a lot more shadowy than chat boards for car enthusiasts. One disturbingly violent paramilitary site remains graven in my memory; but that was an exception. Of the scores of accounts I have set up over the last decade, both for the CIA job and others, I deleted nearly all after a few minutes or days, and they fled my memory soon thereafter. Although I think I would recall a site as thematically and graphically striking as Ashley Madison, it is conceivable I subscribed briefly and have forgotten. Another writer has found herself on the list of shame for similar reasons.
And signing up for Ashley Madison isn’t the only way to get in the dump, since data from other outposts of Avid Life Media, the parent company of Ashley Madison, are in it too. Avid Life owns sites like AdultFriendFinder.com, CougarLife.com, EstablishedMen.com, and ManCrunch.com, which are just places where people, single or not, can meet other people to arrange sex or its antecedents. Reports vary on how many data from the sister sites were leaked, but the consensus is that it was a lot. In other words, a large number of people whose only “crime” was to express a desire for sex, have had their names (and possibly sexual predilections) revealed and associated with an adultery website, their passwords and credit cards put within the grasp of identity thieves, and all the rest.
Like others in our situation, my wife and I tried to learn more about the account attached to my email address by logging on to the various Avid Life sites. At each, we were told no account was linked to my email; if one had existed, it had since been deleted. Had we been braver or more foolhardy, we might have ventured into the dark web and tried to access the raw data, which could perhaps tell us which website my email was attached to, when the account was opened and closed, from which IP addresses the account had been accessed, and whether one of my passwords or credit cards had been compromised. But the ominous threats of encountering ruinous malware in the dark and among the torrents held little allure for us. Nor were we eager to possess stolen goods—that, apparently, is a prerequisite for seeing your own data, since you have to download everyone else’s stolen data along with it.
A final option was to use the services of the one company, Trustify, that has been offering to do the dark-web work for the worried or the curious. Trustify was charging $268 for a typical Ashley Madison inquiry, which seemed ridiculously high for what amounts to copying and pasting—technically skillful copying and pasting, but copying and pasting all the same. More odiously, when someone uses Trustify’s email search feature and discovers an address in the Ashley Madison pile, Trustify sends a note to the tainted address, both letting the recipient know his or her fate and offering the services of one of Trustify’s “experienced investigative consultants.” Trustify defends this: they’re just benevolently telling people they’re being checked out—wouldn’t you want to know? But since they tell only those people who come up “dirty,” not those who come up “clean,” you could be forgiven for thinking the company’s motives are more financial than informational.
My wife and I decided we could wait. Knowing more would not affect what we needed to do, which was change our passwords, scrutinize our credit card bills, and attend to the other rituals of the age of internet insecurity. In a month or two, we would poke around again. By that time, Trustify might have dropped their prices, or, quite possibly, the data might be available in all its tawdry glory on the workaday net. In the meanwhile, I will anticipate more stimulating emails. Even as I write, Myrtle Nelson has sent a “Hot MILF teacher request.”