Supporters of the Islamic State, or ISIS, around the world gather online, becoming members of virtual communities in much the same way any of us might join online groups focused on some common interest. The videos, audio messages, letters, chatter and know-how that they then share are much more sinister than typical online hobbies, though. They may ultimately inspire terrorist acts by individuals who have no prior history of extremism, no formal cell membership, no direct links to leadership.
How does this online support for ISIS manage to not just survive but thrive – even in the face of plenty of online anti-ISIS opposition?
The importance and urgency of this question couldn’t be greater, particularly given the uncertainties surrounding recent terrorist attacks by “inspired” individuals in the United States, as in San Bernardino and Orlando.
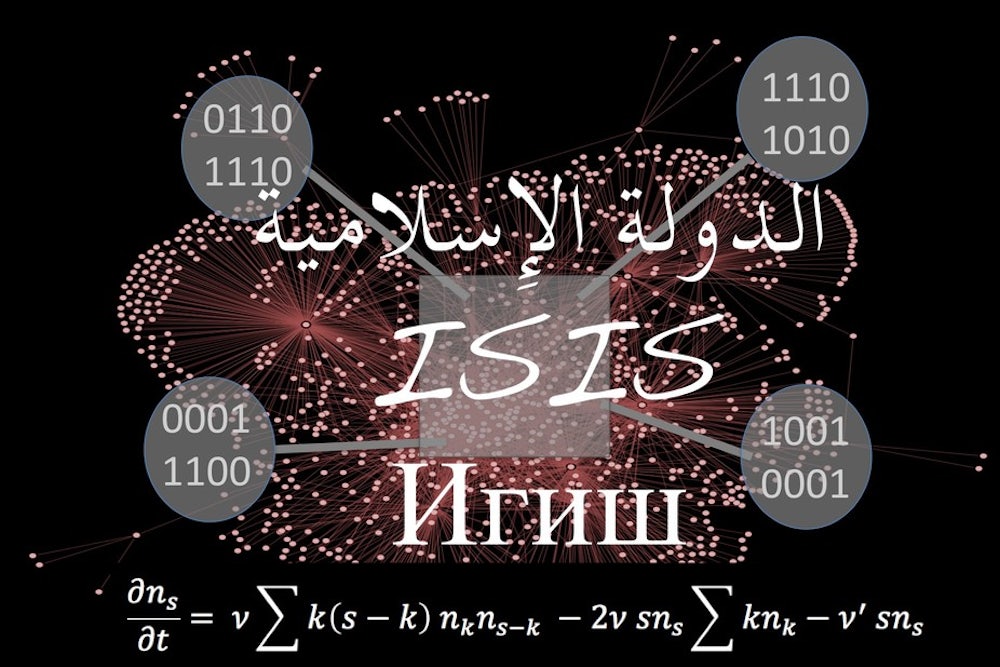
My colleagues and I at the University of Miami’s Complexity Initiative decided to tackle this question of what makes pro-ISIS online support tick. By intensively analyzing online data we’ve been collecting continuously since 2014, our goal was to decode the online “ecology” of ISIS supporters. Could we even go a step further and use what we learned to make accurate predictions about real-world attacks?
Online fieldwork: hunting out the data
The key challenge we faced as researchers was how to obtain the data. Many social media sites quickly shut down any pro-ISIS activity, meaning we found negligible amounts of pro-ISIS activity on Facebook, for instance.
But when we looked at other social media sites around the world, we found that some were slower to shut down pro-ISIS activity – probably because finding such aggregates and shutting them down requires significant amounts of resources and time. We assembled a multi-disciplinary team with expertise across languages.
After many dead ends, we found that the social media site VKontakte was ideal for our pro-ISIS analysis. It is the most popular online social networking service within central Europe and has more than 350 million users worldwide. Being based physically in Russia, it has a high concentration of users of Chechen origin in the Caucasus region, near ISIS’ main area of influence in the Levant. And ISIS is known to have spread significant amounts of propaganda among the Russian-speaking population.
We started off by manually identifying relevant pro-ISIS narratives using hashtags in multiple languages – for example, expressions of support or positive references to particular ISIS actions. Then we’d trace them to the underlying online “aggregates.” An aggregate is an ad hoc virtual community that anyone can create on social media sites – imagine a group on Facebook focused on a particular sports team. Users can become members if they’re fans, and then share significant information and material about that team.
The same applies for pro-ISIS aggregates, but now in support of ISIS rather than a sports team. To be included on our pro-ISIS list, an aggregate had to explicitly express its support for ISIS, publish ISIS-related news or propaganda and call for jihad in the name of ISIS.
We then developed software Application Programming Interfaces (APIs) that expanded our list of aggregates by means of automated searches on hashtags or relevant words. For example, we might have initially found an aggregate called ILiveForISIS manually. We’d scour ILiveForISIS for keywords and content that the APIs could then use to search and uncover new aggregates.
When the APIs eventually started turning up ILiveForISIS together with other pro-ISIS aggregates already on our list, we would know that we were reaching closure. At that stage, while not perfect, we were confident that we had captured a high proportion of what actually existed online.
Eventually we found 196 pro-ISIS aggregates involving 108,086 individual followers between January 1 and August 31, 2015. Membership ebbed and flowed each day; on the most active day, the total number of follower links reached 134,857.
This process of data collection, analysis and modeling provided us with a living road map of online pro-ISIS activity. Next, we needed to develop a mathematical theory for pro-ISIS online support that was in good quantitative agreement with the raw online data.
An online ecosystem of pro-ISIS sentiment
Our research revealed an ultrafast ecology of self-organized aggregates that share operational information and propaganda, and whose rapid evolution drives the online support.
During a typical period of a few weeks, aggregates would appear and disappear sporadically, with their total number changing relatively slowly. Over a particular set of months, however, we found that the rate at which new aggregates appeared started to increase very rapidly – in technical terms, it diverged. Its peak coincided almost exactly with the unexpected onset of real-world attacks on Kobane in Syria by ISIS fighters.
Curiously, we had found a similar divergence in the rate at which new aggregates appeared just before the onset of another unexpected burst of events (this time, non-ISIS civil unrest events) in Brazil in 2013. This suggested to us that an explosion in the rate at which new aggregates appear in the online world can act as an indicator of conditions being right for a burst of attacks in the real world.

We also found that the evolution of this aggregate ecosystem follows a rather precise mathematical form. As the size – the number of members – of each aggregate evolved over time, it produced a familiar shark-fin shape. It’s the same shark-fin shape we find in the natural sciences when groups of interacting objects (particles, animals) follow a process of coalescence and fragmentation.
In other words, these groups of ISIS supporters come together (coalescence) and break up (fragmentation) like fish in schools or birds in a flock might. There’s one difference, though. When they break up, they fragment completely because some external, anti-ISIS entity or online moderator has shut them down. That’s why you see the abrupt drop-off like the edge of a shark fin.
From math model to real-world disruption
These pro-ISIS aggregates are leaderless, self-organized entities that change rapidly over time. But now that we’ve identified a rather precise mathematical equation that describes their evolution, we can start to think about how to intervene.
To start, the main implication of our work is that once you identify the aggregates, you have your hand on the pulse of the entire organization. Instead of having to sift through millions of internet users and tracking specific individuals, an anti-ISIS agency can simply follow the relatively small number of aggregates to gauge what is happening in terms of hard-core global ISIS support.
As these ISIS supporters coalesce over time into aggregates, anti-ISIS agencies have an opportunity to step in and break up small aggregates before they develop into larger, potentially powerful ones. One concern is that if anti-ISIS agencies – be they government-based, private hackers or online moderators – aren’t active enough in their countermeasures, pro-ISIS support could quickly grow from a number of smaller aggregates into one superaggregate.
Our model also warns that if aggregate shutdown rates drop below a certain critical value, any piece of pro-ISIS material will then be able to spread globally across the internet. A low shutdown rate allows an aggregate time to internally develop ideas, content and plans. Then when it’s eventually shut down and the members scatter, they take this content with them to the new aggregates they eventually join.
Our analysis of the data suggests that the rate of creation of aggregates proliferates in a specific mathematical way preceding bursts of real-world attacks. This means monitoring such proliferation can help predict when conditions are favorable for future real-world attacks. If anti-ISIS trackers are on the lookout, a big online surge can therefore be an early warning that could be used along with additional intelligence to thwart a planned terrorist action.
But perhaps most importantly in light of the massacre in Orlando, our research also suggests that any online “lone wolf” actor will truly be alone only for short periods of time. Since we observed that people with serious interest in ISIS online tend to coalesce into these aggregate groups, any such lone wolf was likely either recently in an aggregate or will soon be in one.
As for the future, even if pro-ISIS support moves onto the dark net where open access is not possible, or if a new entity beyond ISIS emerges, our results should still be relevant. The mechanism we’ve identified and theory we’ve developed appear to capture a basic process of human online behavior. Going forward, it can be used to help describe not only pro-ISIS online activity, but also that of any future extremist group or organization.
![]()
This article was originally published on The Conversation. Read the original article.